Silent KYC: Deep Dive
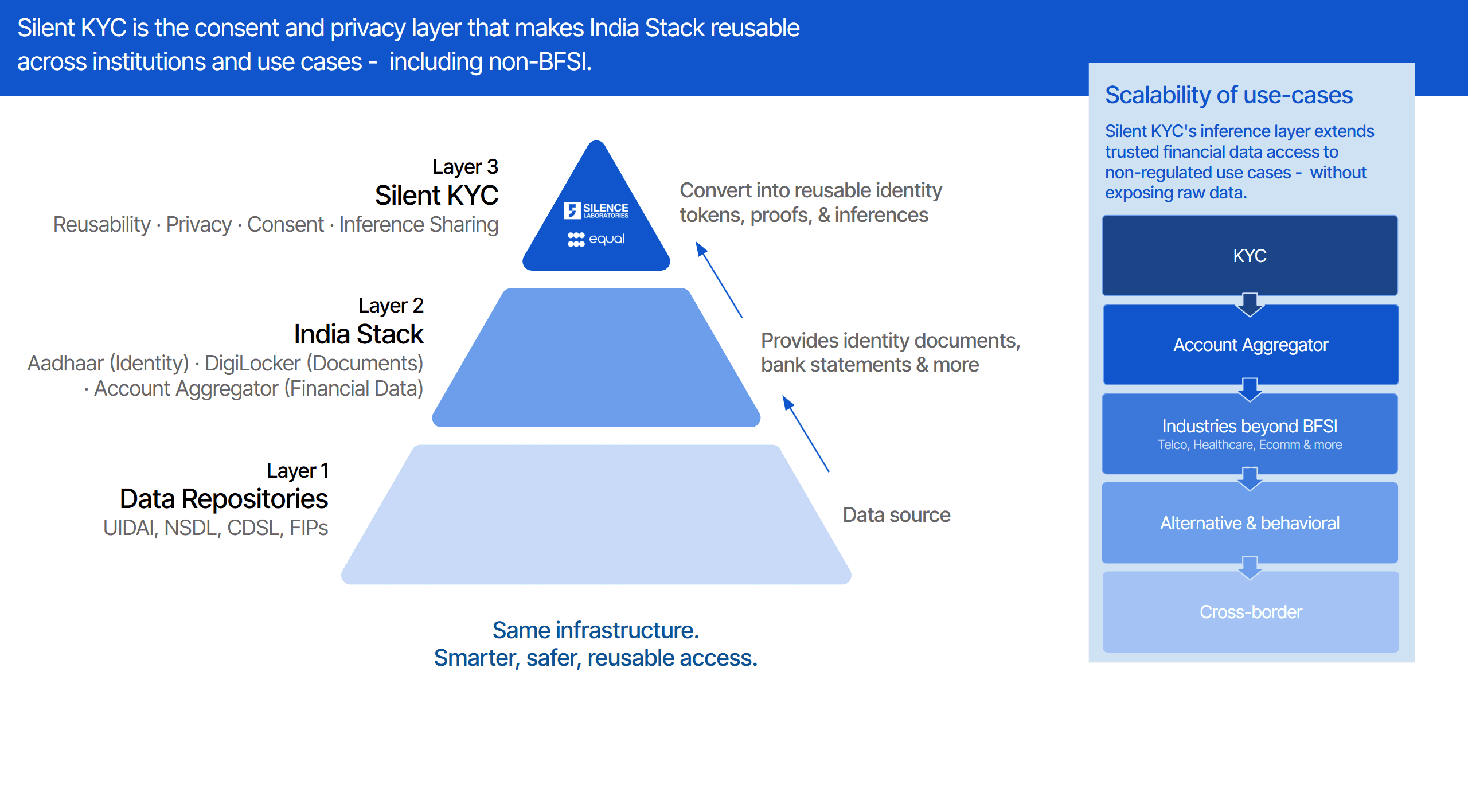
Silent KYC is India's first user-controlled privacy-preserving identity & data wallet infrastructure. An interoperable, privacy-first protocol where verification replaces disclosure, and users own their data, completely.

Written by
Kush Kanwar
Insights
May 4, 2026

SHARE
You apply for a loan or open a new account, and once again you’re asked to upload full bank statements and identity documents. The process feels repetitive and invasive, but you go ahead because there’s no alternative.
Later, you’re spammed with calls offering you pre-approved credit cards, investment plans and other financial products.
In today's verification journey, proving who you are means sharing everything - raw Aadhaar scans, bank statements, salary slips, to every institution, every single time. The data you share can travel beyond the original intent, sits in systems which cannot be audited, and offers no recourse to users.
Silent KYC changes this entirely.
Powered by Silence Laboratories' Cryptographic Computing Virtual Machine (CCVM), Silent KYC is a cryptographically secured, interoperable protocol built on top of India stack. Users create reusable identity and financial proofs once, and share only what is necessary, only with who they choose, and only for the purpose they explicitly approve. Raw data never moves. Not to the requesting institution. Not even to the verification provider.
This marks a shift from data sharing to proof & inference sharing, where users remain in control not just of what is shared, but also how it is used.
VERIFICATION WITHOUT DISCLOSURE
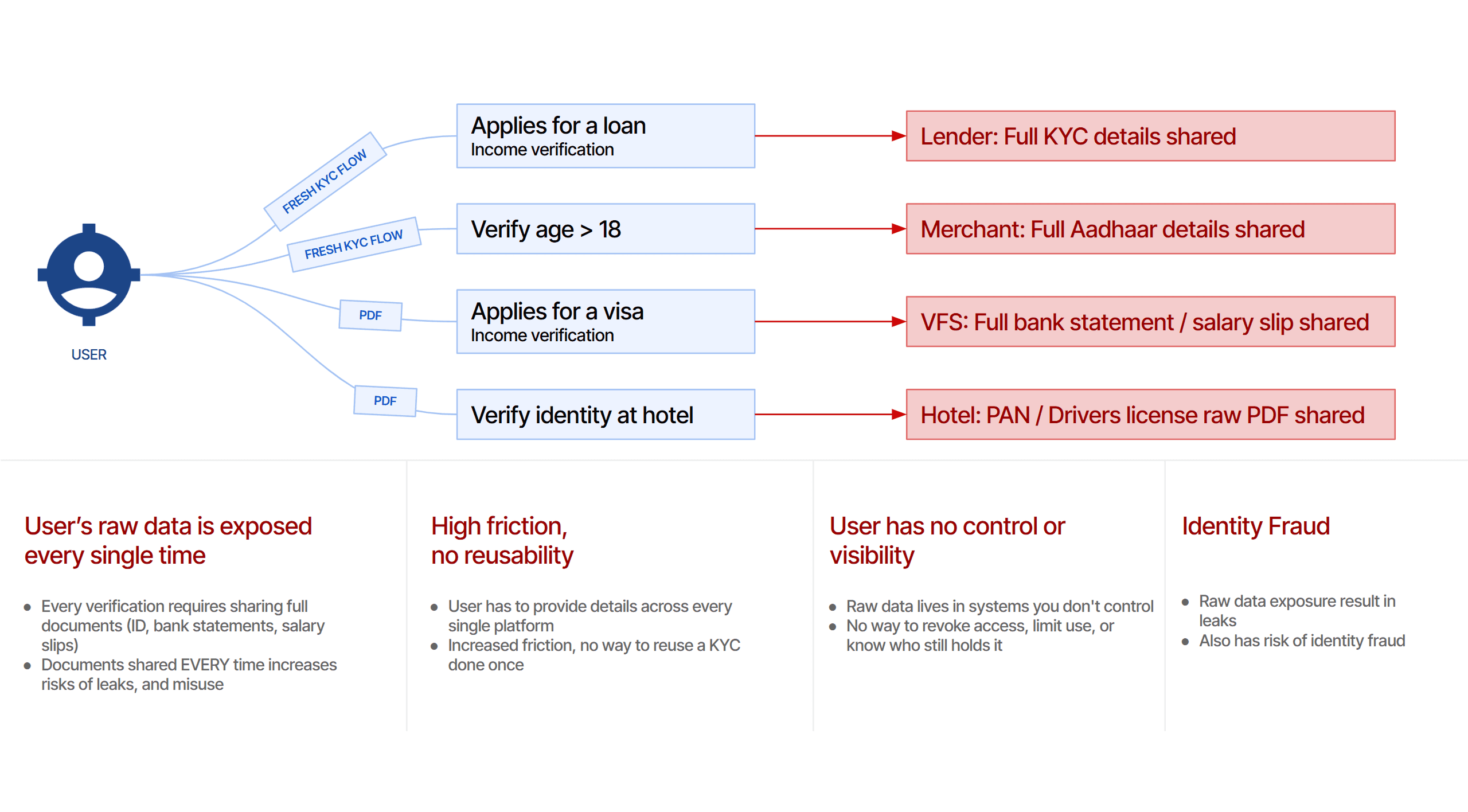
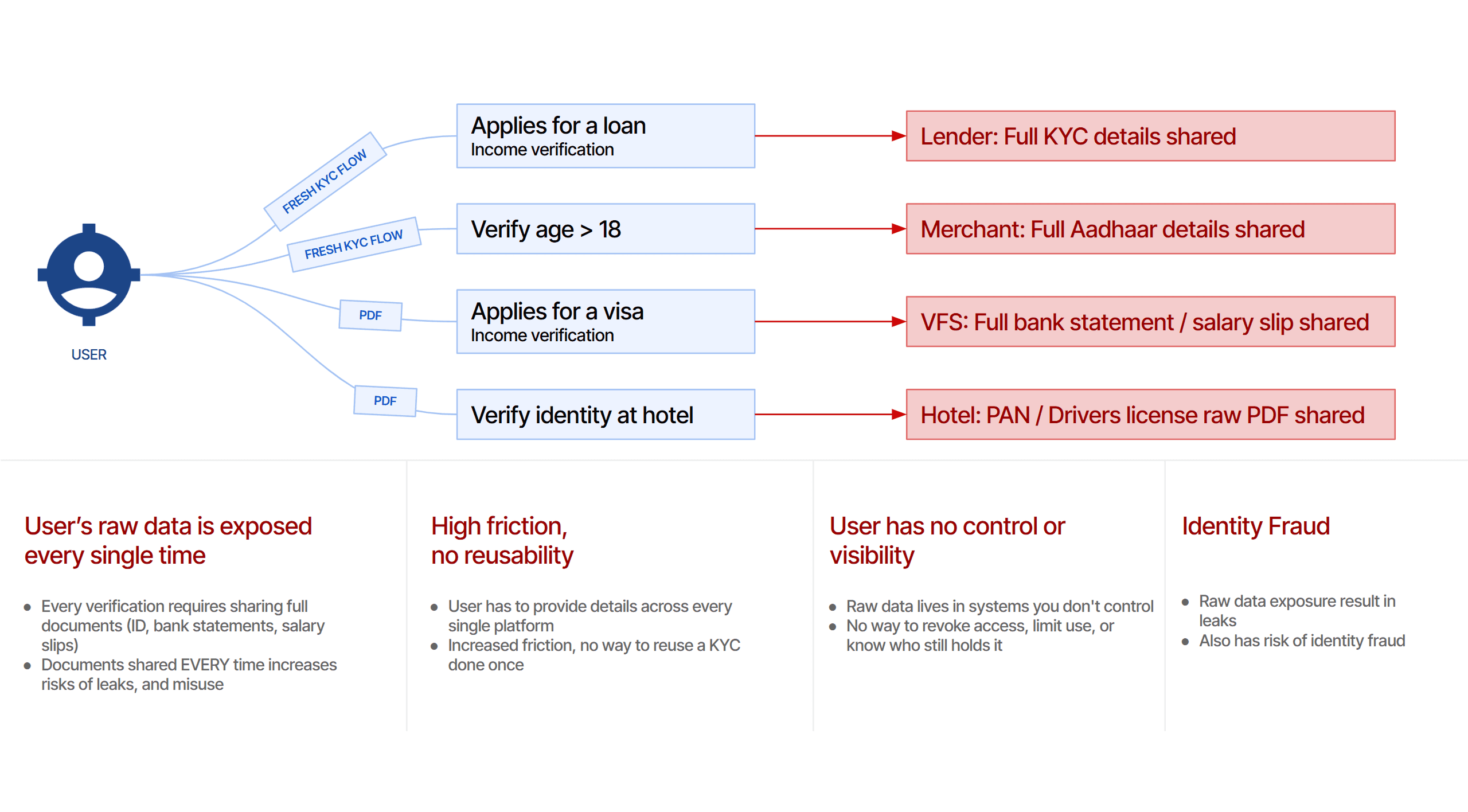
Today's KYC and identity verification systems were built as data-transfer mechanisms.
In the current KYC methods, a fresh user verification is required for every requesting entity which leads to raw data exposure every single time the user is required to prove identity, or financial status. There is no way to share proof of identity without sharing the underlying raw data.
For users, this means high friction during onboarding, lack of control over their own data and risk of data leakage and misuse. For institutions, this translates to loss of business opportunities due to drop offs, and lack of verified data from trusted sources to screen customers, leading to potential fraud incidents.
Silent KYC fundamentally reimagines this model. Institutions receive cryptographically verified proofs and computed inferences, not documents, not raw records, generated directly from trusted issuers like UIDAI, DigiLocker, CKYC, and the Account Aggregator network.
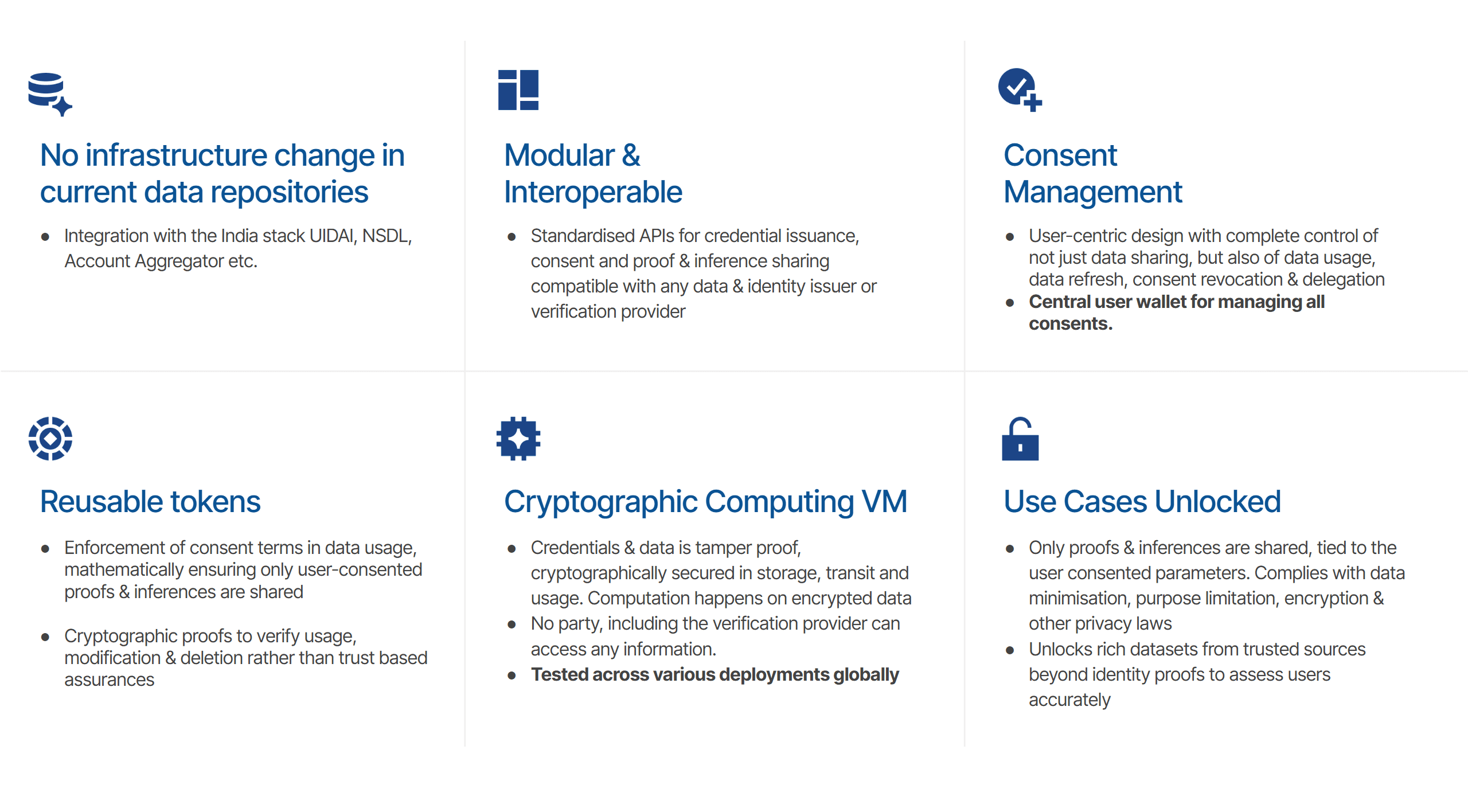
INTEROPERABLE & MODULAR PROTOCOL
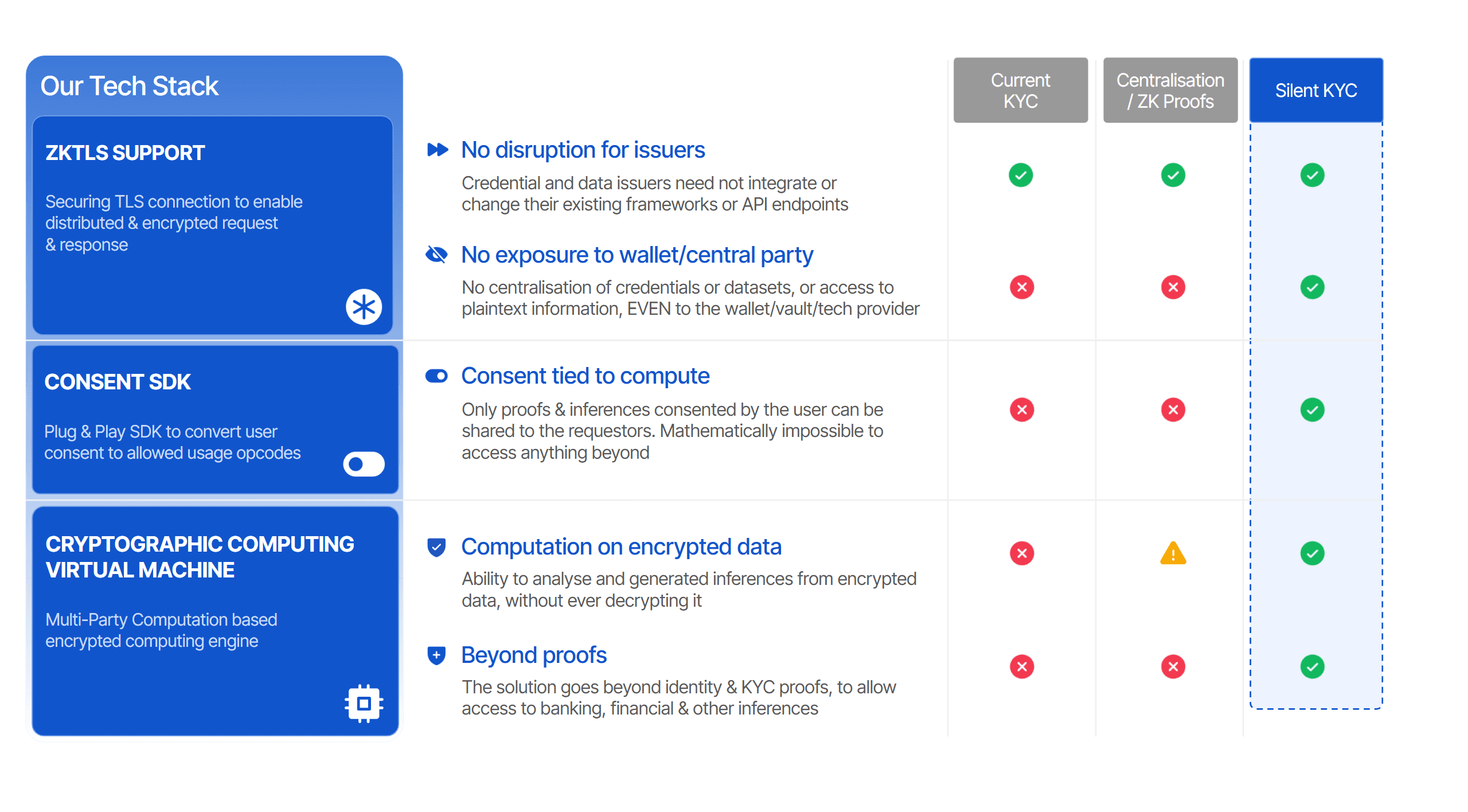
At the heart of the system is Silence Laboratories' CCVM, built on Multi-Party Computation (MPC) and Zero-Knowledge Proofs (ZKP). The CCVM processes identity and financial data in fully encrypted form, computation happens without decryption, releasing only the specific proof or inference the user has authorised. It is mathematically impossible for any party, including Silence Laboratories or the data fiduciaries, to access anything beyond what the user explicitly consents to.
Unlike traditional or tokenisation based approaches, Silent KYC eliminates the need for central vaults or trusted intermediaries, replacing them with mathematical guarantees of privacy and purpose limitation.
"The goal wasn’t to replace existing ecosystems, but to strengthen them, so institutions can collaborate and verify, without ever needing to see the underlying data"

Jay Prakash
CEO & Co-founder, Silence Laboratories
Silent KYC is not a proof of concept. The protocol has been natively integrated and tested across the Indian Account Aggregator framework, US Open Banking providers including Plaid, and cross-border data frameworks. It was deployed in Project Mandala with the BIS, and won the G20 2025 TechSprint jointly organised by the South African Reserve Bank (SARB) and the BIS for enabling cross-border credit data portability with Proxtera.
DATA TRULY IN THE USER'S HANDS
Equal is one of the initial design partners for Silent KYC, contributing the user-facing wallet infrastructure that helps make the framework tangible and accessible. Through the Equal wallet, users can:
Create their identity and financial inference tokens once, across UIDAI, NSDL, Account Aggregator, and other India Stack data sources
View, manage, delegate, and selectively share credentials, with full visibility into who holds their data and for what purpose
Set granular consent parameters: what is shared, how it may be used, for how long, and under what restrictions
Revoke or modify consent at any time, with cryptographic enforcement, not just a policy promise
Reuse verified credentials across banks, NBFCs, insurers, fintechs, and any participating institution
As an early partner, Equal also brings proven scale and distribution, powering over 1.5B+ annual data transactions across 350+ enterprise customers. Its extensive coverage across identity and data sources helps ensure Silent KYC is built on robust, widely adopted infrastructure. Importantly, Silent KYC is designed as an open, interoperable framework—any wallet provider, financial institution, or ecosystem participant can integrate and build on it.
THREE FEATURES THAT SET SILENT KYC APART
No Exposure. No disruption in existing issuer infra.
Unlike traditional or centralised models, there is no aggregation layer or plaintext visibility of data. Data remains with the issuer, eliminating entire classes of breach and misuse.
Silent KYC sits as a layer between issuers and requesters, leveraging existing verification flows without changing or disrupting current issuer APIs and infrastructure.
Consent, Enforced in Compute
Consent is dynamically enforced during computation. User approvals are translated into machine-enforceable policies that strictly govern what can be computed, making it mathematically impossible to derive any insight beyond what has been explicitly consented.
Computing on encrypted data
User consent is converted into cryptographic opcodes at the moment of authorisation. The CCVM executes only what consent permits on the encrypted data itself, with purpose limitation, data minimisation, and usage restrictions are built into the code.
Beyond simple identity proofs, this unlocks richer, privacy-preserving inferences, such as income verification or risk signals, expanding the scope of KYC from verification to intelligent, secure decisioning and consequently reducing identity related fraud risks.
This is not a privacy toggle in an app settings menu. It is mathematically provable control over personal data.
ENABLING RICHER, PRIVACY-FIRST USE CASES
Silent KYC strengthens existing use cases by enabling access to richer, verifiable signals without increasing data exposure. At the same time, it unlocks entirely new use cases by making trusted data accessible to entities that previously could not obtain or handle it.
Lending & Insurance: Better underwriting using verified income and financial behaviour signals
Fraud & Risk: Stronger detection using identity and cross-source behavioural insights
Gig Worker Onboarding: Income verification without requiring formal payslips
Rentals (Tenant Verification): Verified identity and financial health without raw documents
Visa Applications: Proof of funds and travel eligibility without sharing statements
Hotel Check-ins: Seamless identity verification without handing over ID copies
Here’s a walkthrough of the demo!



