Institutional-grade solutions to compute & collaborate, without exposing private data

USE CASES
Encrypted Computing At Scale
PRODUCT LINEUP
Silence provides infrastructure
for protecting private data and secrets at scale

Silent Shard
End-to-end MPC as a service
Superior performance
15 -30x faster algorithms, compared to competition.
Future proof protocols
Global first production implementation of OT based DKLs23 MPC-TSS algorithm.
Transparent by design
Native integration & on-prem deployment for simplified risk assessment, compliance & customizability.
Silent Compute
Privacy preserving computations over distributed data
No data movement
Data always stays at the source, compute is done only on inferences.
Ensure consent-bound usage
Cryptographically secured with transparent & auditable consent mechanisms.
Comply with regulations
Navigate privacy & regulatory compliance across jurisdictions.


Cryptographic Computing Virtual Machine (CCVM)
Secrets Management and Data Privacy Engine
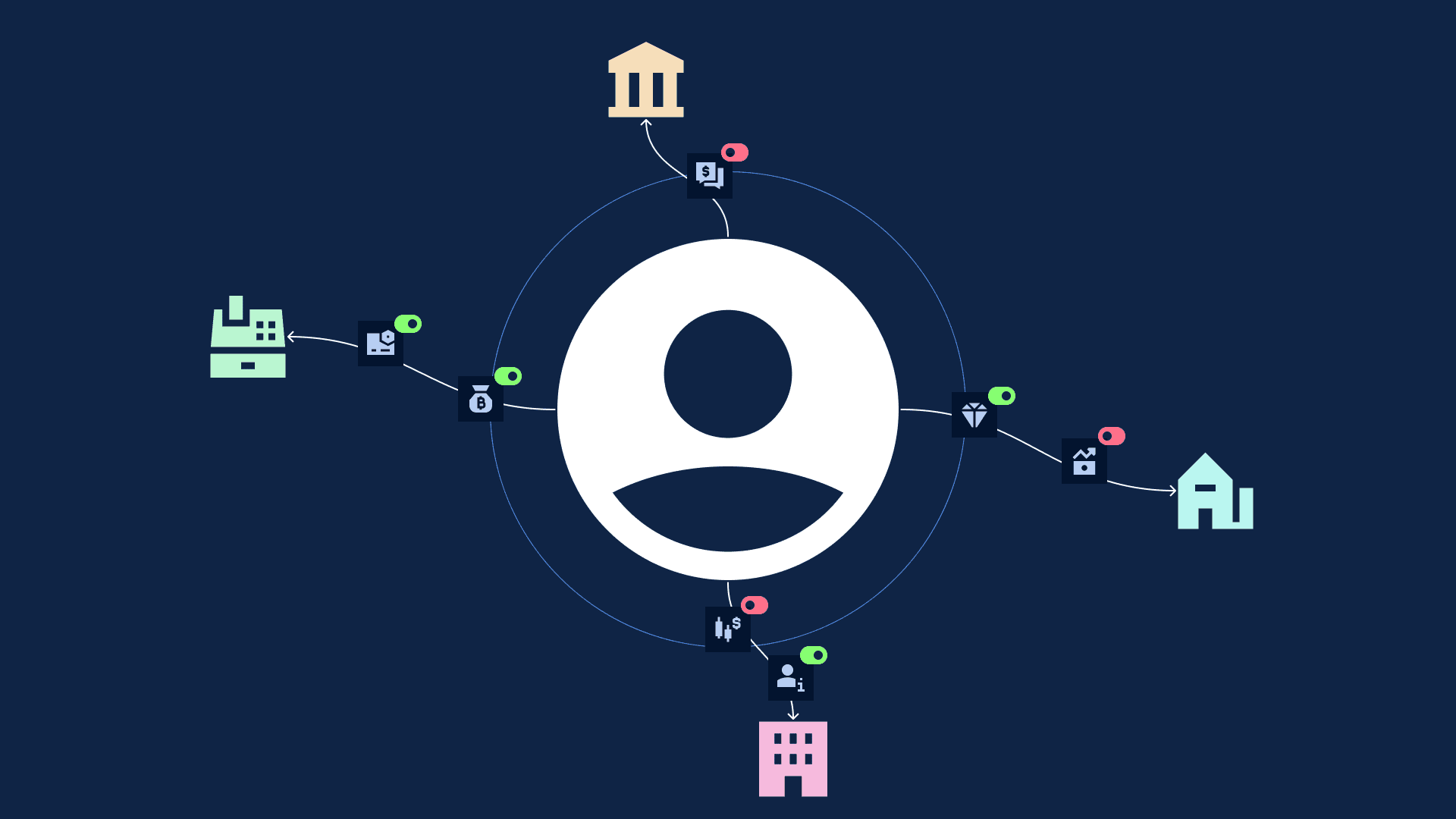
Distributed Authorisation
Create authorisation signatures and tokens without single point of failure of private keys
Private Inference and Collaboration
Create inference on encrypted data
Trustless Policy Engine
Enforce transaction and compute policies and consents with audit trails and verifiability
Global experts in cryptography
50+ contributors
Distributed globally in 18+ countries
10+
Tier 1 publications
2
R&D Centers