
Privacy Preserving Anti-Fraud Consortium
Collaborate with industry peers to proactively detect and prevent fraud, without moving data outside your environment.
Consortium improves fraud screening while ensuring data protection across industries

AML
Screen customers during onboarding by assessing risk indicators derived from activity across consortium members
Payment aggregators
Assess merchants against members’ negative lists to determine prior fraudulent activity across the consortium
Gig platforms
Safeguard your proprietary datasets and detection models while empowering institutions to fight fraud confidently
Internal fraud risks for gig platforms scaling with a 12M+ workforce
Account renting / ban evasion
AI fake image claims
Platform-hopping
+more
Leading to
Direct revenue leakage
Pilferage costs
Consumer trust erosion
Operational loss
+more

Fraud detection
Unlock richer datasets to proactively identify fraudulent activities and understand customer financial behavior to detect anomalies.
Operational efficiency
Reduce false positives, manual delays, costs, and redundant checks to improve operational efficiency.
Privacy and compliance
Comply with privacy & fraud/AML regulations while ensuring zero exposure of customer information to maintain competitive edge.
Privacy enabled network effects
Eliminate trust gaps to encourage active participation and make the system more effective.
Features
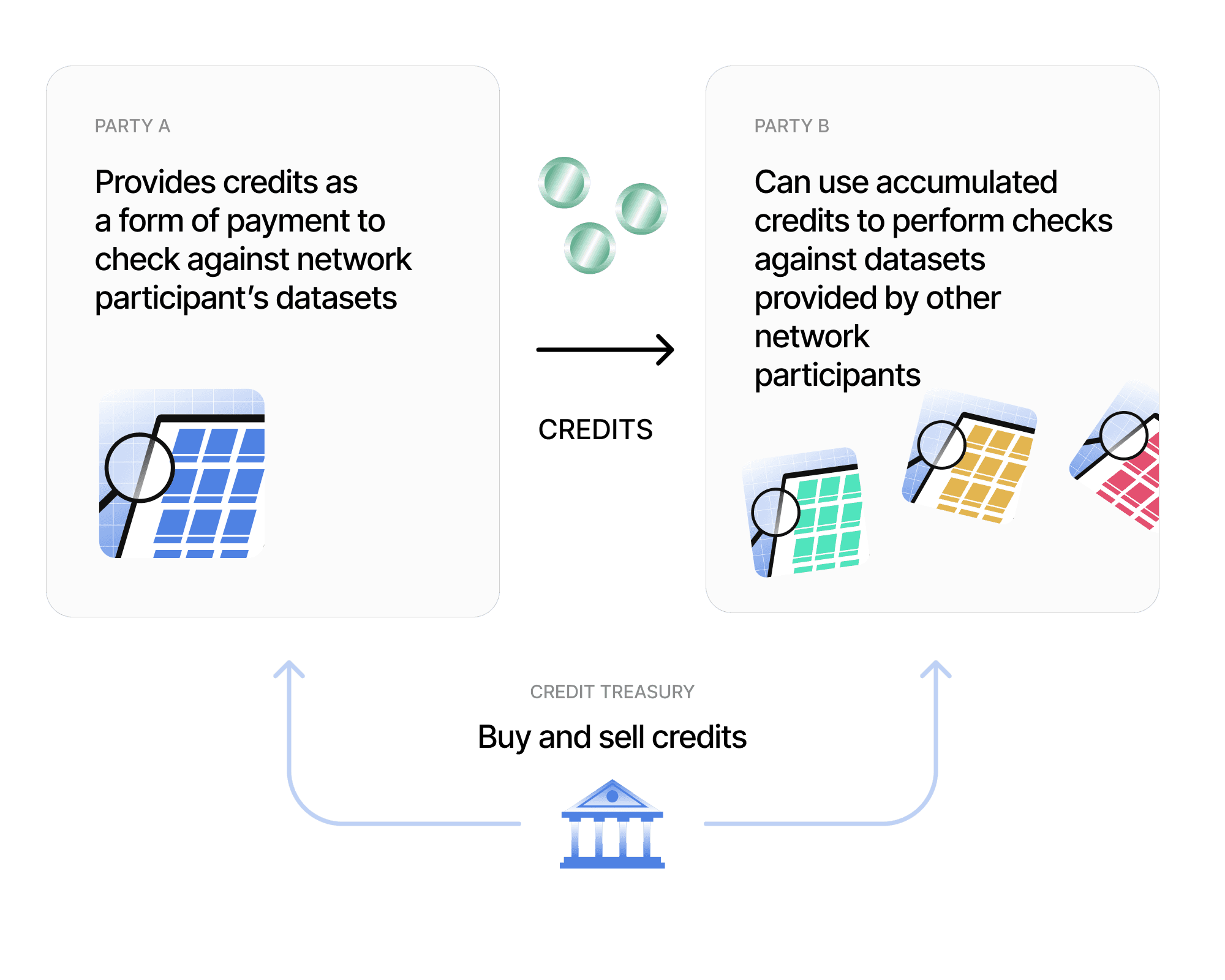
Economics and governance
Provides incentives for larger players to join the network
Makes scraping attacks uneconomical
Ensures players update / maintain quality of data
Governance council can adjust value of credits to align incentives
Resources





