Private APIs: The Missing Infrastructure Layer for KYC, Verification & Trust
Surepass joins Silence Laboratories as a preferred launch partner to bring privacy preserving “Private APIs” to KYC and verification workflows. Together, the companies are enabling encrypted, inference-only verification without exposing customer identifiers or sensitive data.

Written by
Kush Kanwar
Insights
Feb 3, 2026

SHARE
TL;DR: Surepass joins Silence Laboratories as a preferred launch partner to bring privacy preserving “Private APIs” to KYC and verification workflows. Together, the companies are enabling encrypted, inference-only verification without exposing customer identifiers or sensitive data.
This launch reflects an early production deployment of Private APIs within live verification workflows. While the initial integration is with Surepass, the underlying architecture is designed to support a broader set of verification and trust providers as privacy expectations and regulatory requirements evolve.
Today’s digital economy runs on APIs. Payments, onboarding, verification, fraud detection, credit decisions, everything today is mediated through third-party APIs.
But there’s a fundamental problem hiding in plain sight: To get a simple insight such as a “yes/no” answer, organisations are forced to reveal far more than they should.
Customer identifiers. Sensitive attributes. Timing, scale, and intent.
This wasn’t a big issue when data volumes were small and ecosystems were closed. But at scale & with privacy regulations globally now moving from theory to enforcement, it’s becoming a serious architectural risk.
Verification Needs Data, Compliance Restricts It
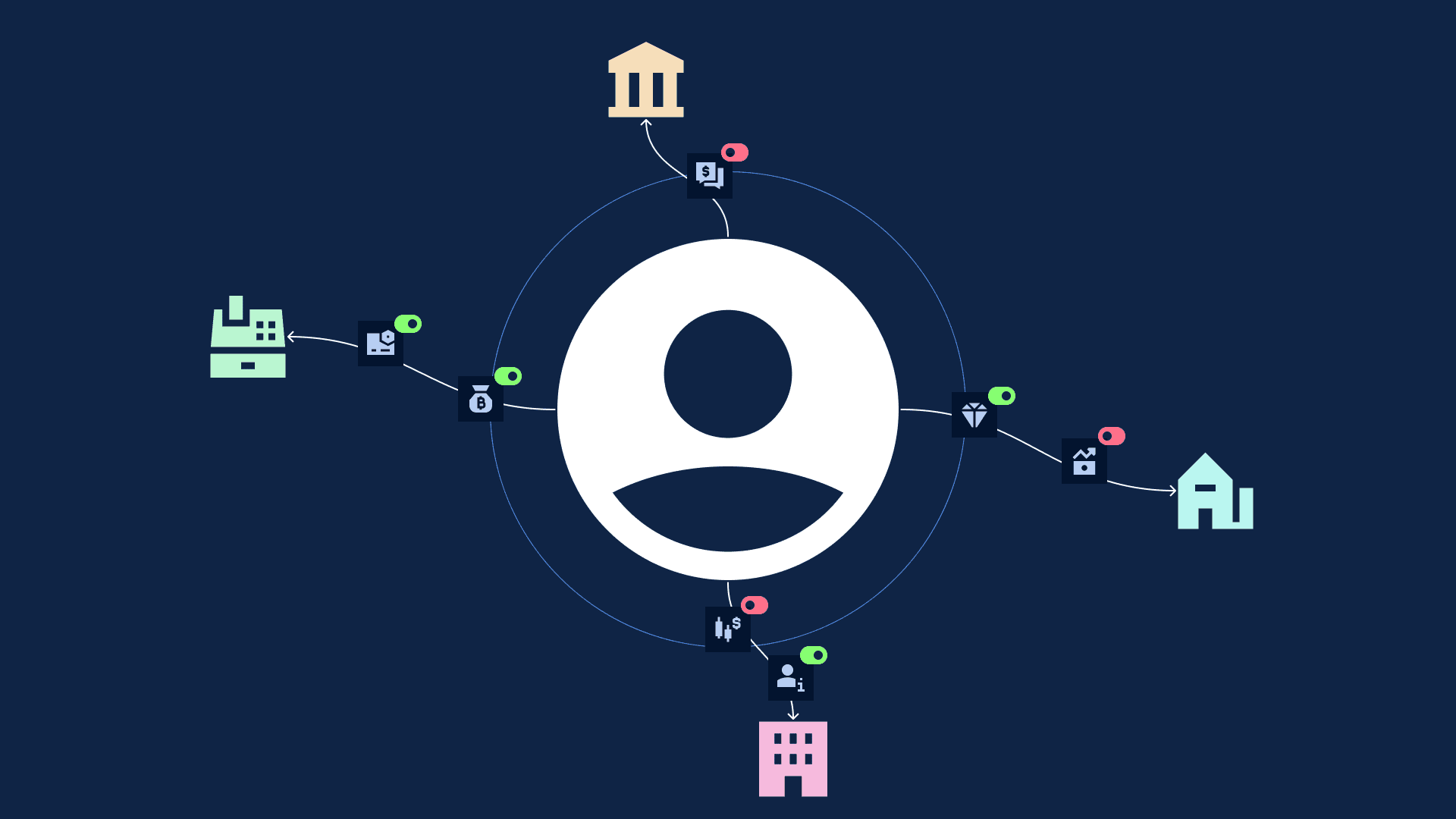
Most KYC, verification, and fraud workflows today look roughly like this:
A bank, fintech, insurer, or platform sends customer identifiers (phone, PAN, Aadhaar reference, email, device, etc.)
A third-party provider runs checks on public & proprietary datasets or networks
The provider returns a response (verified/not verified/risk score)
From a product lens, this works. From a privacy, compliance, and competitive lens, it’s increasingly fragile.
Three hard constraints organisations are now facing:
Sensitive identifiers must be shared with multiple parties: Every additional verification step introduces another data exposure surface
More data exists, but cannot be used safely: Organisations want to use richer datasets (telecom, behavioural, transactional, network-level signals), but:
Consent becomes complex & lacks proofs of proper enforcement
On-prem deployments are often not possible
Proprietary datasets cannot be shared without leakage risk
3. Regulation is catching up to reality: Privacy laws don’t just see privacy as a policy issue, they treat it as an architectural obligation.
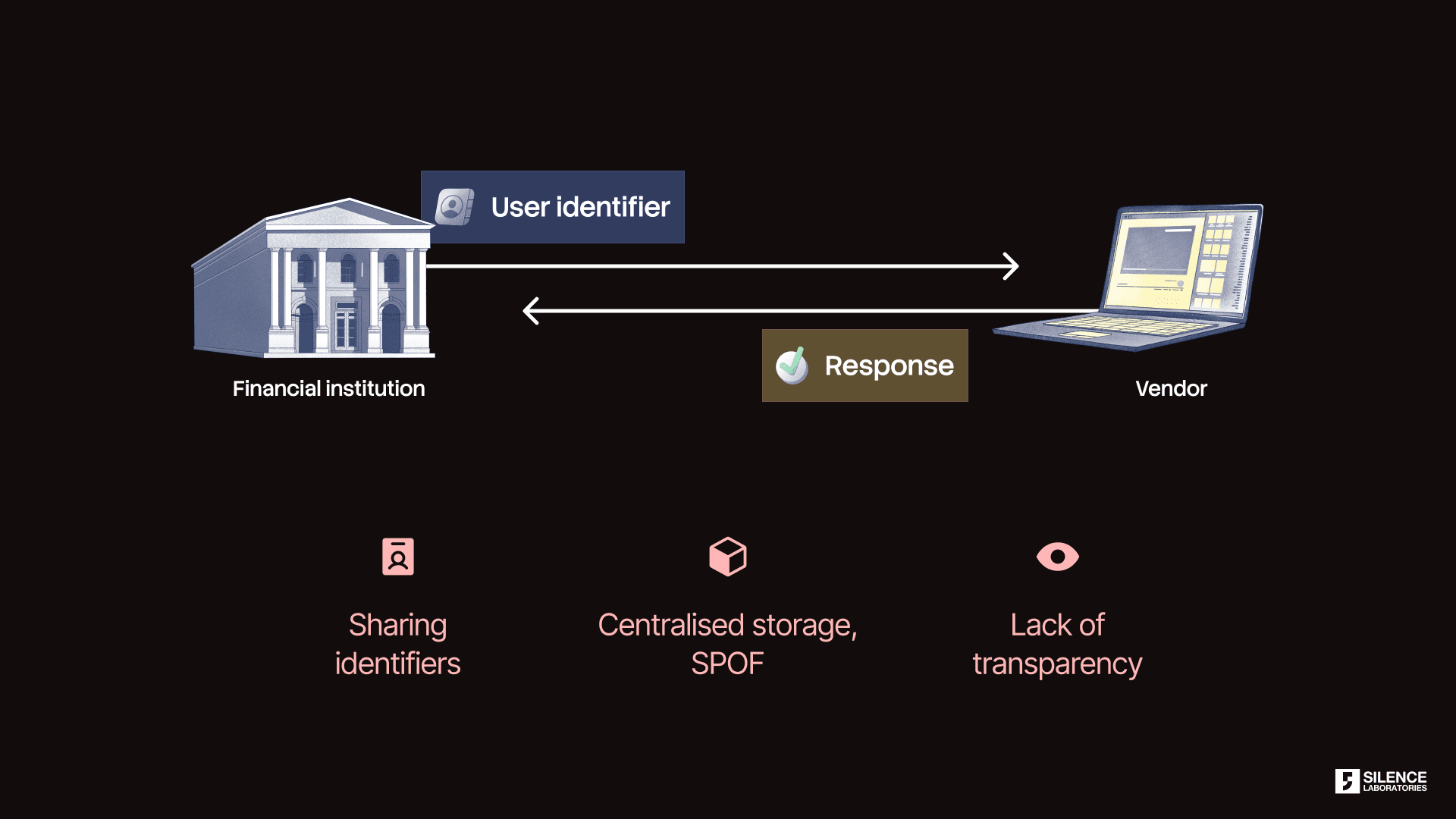
Image 1: Current verification APIs exposes user identifiers to vendors
The result? Teams either under-utilise data, or over share sensitive data and hope legal bilateral contracts or weak privacy mechanisms will save them.
Market Validation: This Is Inevitable
Conversations with organisations across the KYC, verification, identity, and risk space point to a clear market signal: privacy expectations are increasing. Customers are asking for on-prem options, stronger auditability, and proper privacy tooling.
What’s holding adoption back isn’t demand, but the absence of the right infrastructure.
Karan Kapoor, Co-Founder of Surepass Technologies comments: “With data protection moving from policy to enforcement, organisations are being forced to rethink how verification APIs are architected - whether through on-prem preferences, stronger auditability, or tighter control over how data is used. Private APIs represent a necessary evolution, not an optional upgrade”.
Some players know the current model is broken but are hesitant to move first. Some are waiting for clear regulatory signals. Others want on-prem solutions but can’t get access to third party proprietary datasets or insights that way. Most are waiting for a model that satisfies compliance, business incentives, and scale at the same time.
Privacy regulations accelerate this shift, not initiate it. The need already exists.
The Opportunity in Modern Verification APIs
As verification APIs become more deeply embedded in onboarding and risk workflows, they also create an opportunity to rethink how trust is architected. At its core, KYC is meant to confirm eligibility and compliance, not to surface customer lists or broader signals about business strategy or growth patterns.
In traditional integrations, verification workflows naturally carry contextual & commercially valuable information such as potential target customer segments, cohorts with high intent, acquisition pipelines and more.
The lesson is simple: Trust cannot be contractual alone. It must be architectural.
Private APIs enable these privacy-first designs. By separating verification outcomes from visibility into underlying activity, organisations can continue to access high quality verification and risk signals while keeping customer lists, onboarding intent, and growth trajectories within their own control.
Introducing Private APIs: Same Workflows, Different Guarantees
Private APIs don’t replace existing KYC or verification APIs. They reinforce them with visible privacy guarantees.
At Silence Laboratories, this is enabled using Multi-Party Computation (MPC) based Cryptographic Computing Virtual Machine (CCVM).
The idea is straightforward: Exchange inferences, not raw data.
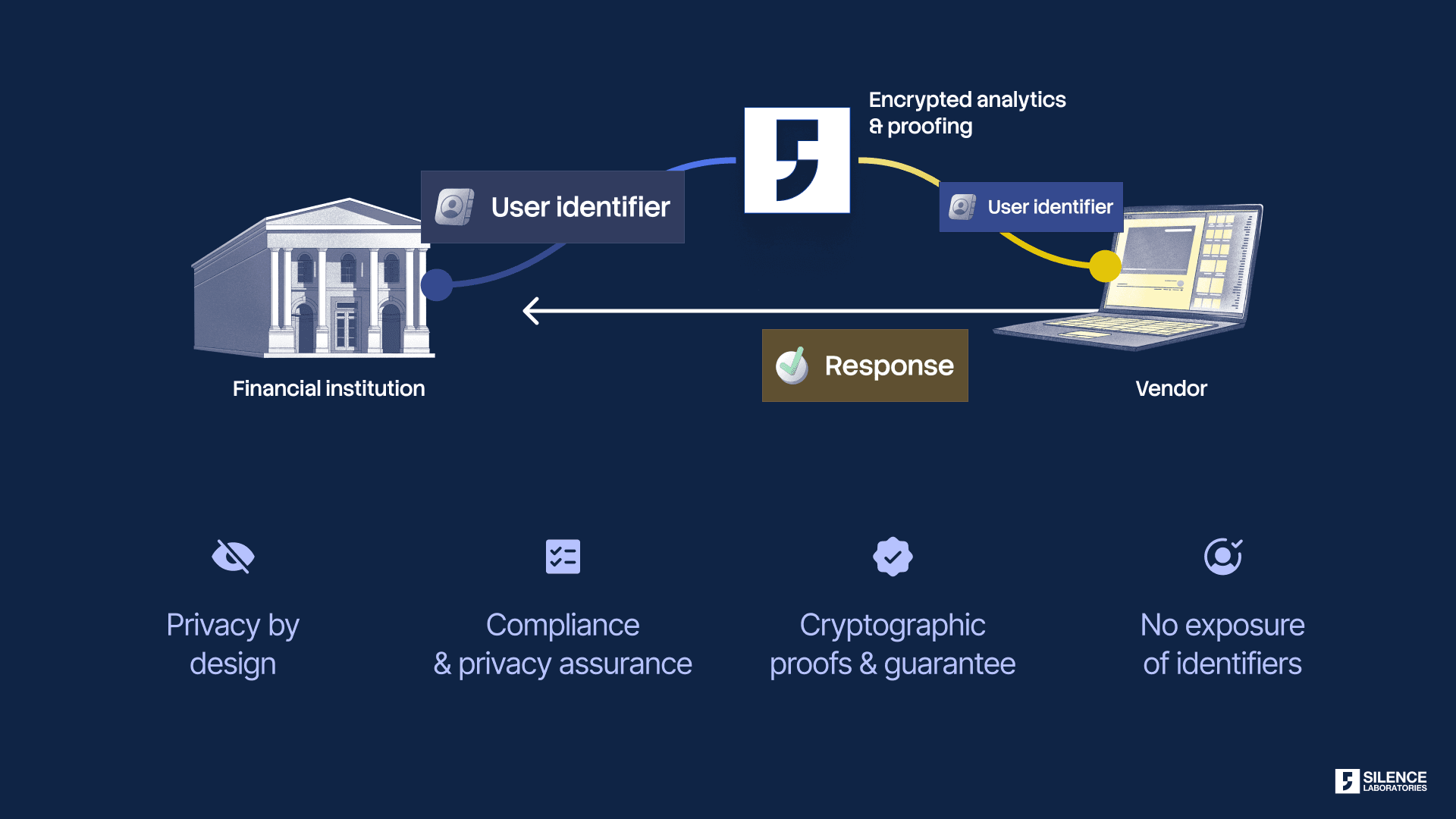
Image 2: Private APIs ensures only inference exchange without revealing user identifiers
How Private APIs work
Silence Laboratories provides a privacy-preserving computation and orchestration layer that sits between financial institutions and verification vendors.
This layer:
Exposes only approved inference outputs
Prevents access to underlying datasets, intermediate states, or model parameters
Enforces auditable, consent-bound and encrypted computation
These inferences can be generated by running the verification organisation’s analytics on its own datasets, or execute its proprietary models on data contributed by demand partners or approved third parties.
Regardless of the configuration, the guarantees remain the same: each party retains full ownership and control of its data and models, raw data never leaves its original boundary, and nothing beyond the final, agreed-upon inference is made accessible.
The result is a set of private APIs that deliver the same business outcomes as traditional integrations, verification, risk signals, and insights, without creating new privacy or competitive exposure.
Unlocking a New Class of Private APIs
Once encrypted computation, not data sharing, becomes the primitive, a wide range of sensitive workflows can be exposed safely through private APIs.
Verification APIs can confirm attributes such as identity validity, account existence, or eligibility without disclosing the underlying identifiers or documents used to perform the check
Fraud and risk APIs can return risk scores, flags, or network-level signals derived from consortium or proprietary datasets, without revealing customer identities or contributing raw events to shared pools
Behavioural and intent APIs can surface patterns, intents, segments, or propensity scores computed over sensitive behavioural data, while ensuring that individual event-level activity never leaves its source boundary
KYC APIs can validate compliance requirements and onboarding checks without turning the onboarding pipeline as a source of competitive advantage leakage
Together, these private APIs allow organisations to access richer intelligence while sharply reducing data exposure, regulatory risk, and competitive leakage.
A Closer Look: Private KYC
KYC is one of the clearest examples of why this shift matters.
Today, KYC workflows often require sharing highly sensitive information such as customer identifiers, documents, demographic attributes, and onboarding metadata with multiple third-party providers (every time one wishes to avail a service).
With Private APIs, that model flips. Instead of transmitting raw identifiers or documents, institutions receive narrowly scoped inferences, such as verification outcomes, risk classifications, or compliance signals, computed on the provider’s side under strict privacy guarantees. The verification is completed, but the identity, onboarding intent, and customer list remain opaque by design.
The outcome is the same from a compliance standpoint, but fundamentally different in terms of privacy, control, and strategic exposure.
If KYC is meant to establish trust, the infrastructure that powers it should not require giving that trust away.
Private APIs are now live
If you run KYC, verification, or fraud workflows at scale, it’s time to rethink the architecture.
Privacy regulations make this unavoidable. Market forces will make it desirable. Private APIs make it possible.
The future of trust infrastructure won’t be built by sharing more data, it will be built by computing on it safely. And the organisations that get there first will have a durable advantage.
Silence Laboratories has onboarded Surepass as its launch partner for private, cryptography-powered verification APIs. Surepass plays a foundational role in India’s verification ecosystem, enabling identity checks, onboarding, and risk workflows at scale.
Together, Silence Laboratories and Surepass are enabling verification and screening through encrypted computation. The key advantage: Surepass or Silence Laboratories never learn about your customer lists or proprietary datasets, while providing rich inferences for verification.
As privacy-preserving computation becomes a foundational requirement for KYC, verification, and risk infrastructure, this model opens the door for verification providers and platforms to expose trusted signals without expanding data exposure. The shift is architectural, and its applicability extends well beyond any single integration.
Experience it firsthand: test the private APIs, see what gets shared (and what doesn’t), and evaluate how this architecture can strengthen your own onboarding, verification, and risk workflows.
Reach out to us at info@silencelaboratories.com to learn more.