Ethereum’s Pectra Upgrade: A renewed convergence for User Accounts with EIP-7702 and MPC
Multi-Party Computation (MPC) is no longer just a theoretical enhancement but a critical necessity, addressing the core security and usability challenges of the upgrade and paving the way for a more secure and user-friendly Ethereum ecosystem.
Insights
May 19, 2025

SHARE
The Ethereum network is on the cusp of another significant evolution with the forthcoming Pectra upgrade; think of it as the network hitting the refresh button for a smoother ride. This upgrade, a synergistic combination of the Prague (execution layer) and Electra (consensus layer) enhancements, aims to deliver substantial improvements in user experience (UX), scalability, and overall network efficiency, including potentially lower transaction costs. This article will delve into how these new powers, if not managed correctly, can introduce significant risks. We will then explore how Multi-Party Computation (MPC) is no longer just a theoretical enhancement but a critical necessity, addressing the core security and usability challenges of the upgrade and paving the way for a more secure and user-friendly Ethereum ecosystem.
Central to Pectra’s impact on user interaction is EIP-7702, a proposal designed to elegantly bridge the long-standing gap between traditional Externally Owned Accounts (EOAs) and the sophisticated functionality of smart contract wallets.
EIP-7702 introduces a novel transaction type that empowers standard EOAs — the familiar Ethereum accounts controlled by private keys — to temporarily behave like smart contracts for the duration of a single transaction, which is a pretty neat trick. This is achieved by allowing an EOA to delegate its authority to a designated smart contract, which then executes operations on the EOA’s behalf.
The immediate benefits are compelling: users can access advanced features such as transaction batching (performing multiple operations like token approval and swap in one go), gas sponsorship (where dApps or other parties can cover transaction fees), and potentially pave the way for more intuitive alternative authentication mechanisms beyond simple cryptographic signatures, like passkeys or biometric verification for transaction authorization. This innovation promises to streamline interactions with decentralized applications (dApps) significantly, making Web3 more accessible and user-friendly without requiring users to migrate away from their existing EOA addresses.
The Double-Edged Sword 🗡️ : Unpacking the Security Implications of EIP-7702
While EIP-7702 unlocks powerful new capabilities and a much-improved UX, it also brings new security considerations to the forefront and highlights some existing challenges; no free lunches in crypto, right?
The most prominent concern is the amplification of the “sign here, drain everything” risk 📄 . With EIP-7702, an EOA grants significant power to an external contract for a transaction. If this delegated contract is malicious, has vulnerabilities, or its behavior is not fully understood by the user, it could potentially execute unauthorized actions leading to asset loss within that transaction’s scope. This also directly aggravates the single point of failure inherent in traditional EOAs 🚨. The EOA’s private key becomes even more critical because all authorization for these powerful, temporary smart contract capabilities stems from this single key. Unlike EIP-4337 based smart accounts, which can be designed with mechanisms for key rotation or social recovery, EIP-7702 does not inherently change the EOA’s fundamental reliance on its one private key. One wrong click on a malicious delegation, or one compromised key, and assets can be drained because all authority still traces back to that single, vulnerable point of failure. The ease with which an EOA can now endow itself with smart contract logic means that while the security of the chosen “invoker” contract is paramount, the security of the EOA’s private key itself becomes an even more critical bottleneck, as there’s no built-in EIP-7702 mechanism to easily swap it out if compromised.
Furthermore, a critical consideration with EIP-7702, as with any system that defines account logic on-chain, revolves around policy visibility 👁️ . When an organization’s transaction authorization rules — who can approve what, under which conditions — are embedded directly onto a public ledger, they become universally observable. While transparency is a cornerstone of blockchain, this specific type of transparency can be a double-edged sword for security. Exposing the intricate details of an institution’s financial controls can inadvertently provide a roadmap for those with malicious intent, highlighting potential attack vectors or pressure points, including social engineering attacks. It’s akin to a bank publicly posting its internal cash handling procedures and staff rotation schedules.
The consequence is often that on-chain policies are kept deliberately simple, perhaps limited to basic multi-signature schemes. This is a compromise, as it doesn’t allow for the rich, multi-faceted policy frameworks that are standard in traditional enterprise security and are necessary for robust asset protection. While advancements like zk-proofs hold future promise for private on-chain logic, their current maturity and cost can be prohibitive.
Lastly, the multichain conundrum 🕸️ persists. EIP-7702 is specific to Ethereum. While it enhances account capabilities on Ethereum, managing abstracted accounts or similar advanced functionalities consistently and securely across a diverse landscape of EVM-compatible chains and entirely different blockchain architectures remains a significant hurdle; it’s still a bit of a wild west out there. This often translates into needing to define, deploy, and maintain separate policy enforcement mechanisms on each chain an organization interacts with, leading to operational overhead and an increased risk of inconsistencies.
MPC to the Forefront: Addressing EIP-7702’s Security and Usability Challenges 🔐
As Ethereum accounts become more powerful through EIP-7702, the need for robust underlying security for the authorizing EOA private key and for intelligent transaction processing becomes more critical than ever; basically, your digital front door needs the best locks. This is where Multi-Party Computation (MPC) technology offers compelling solutions.
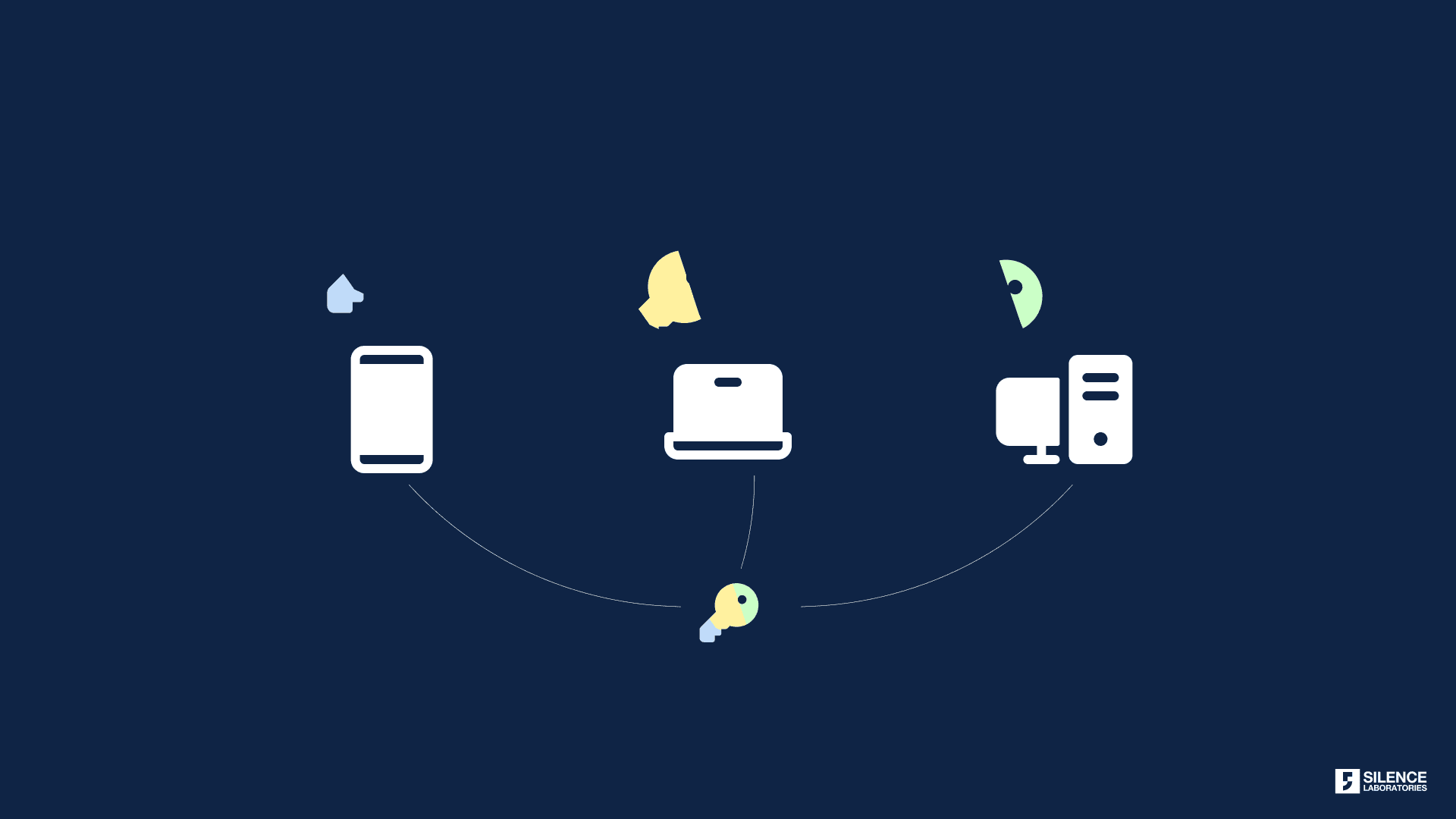
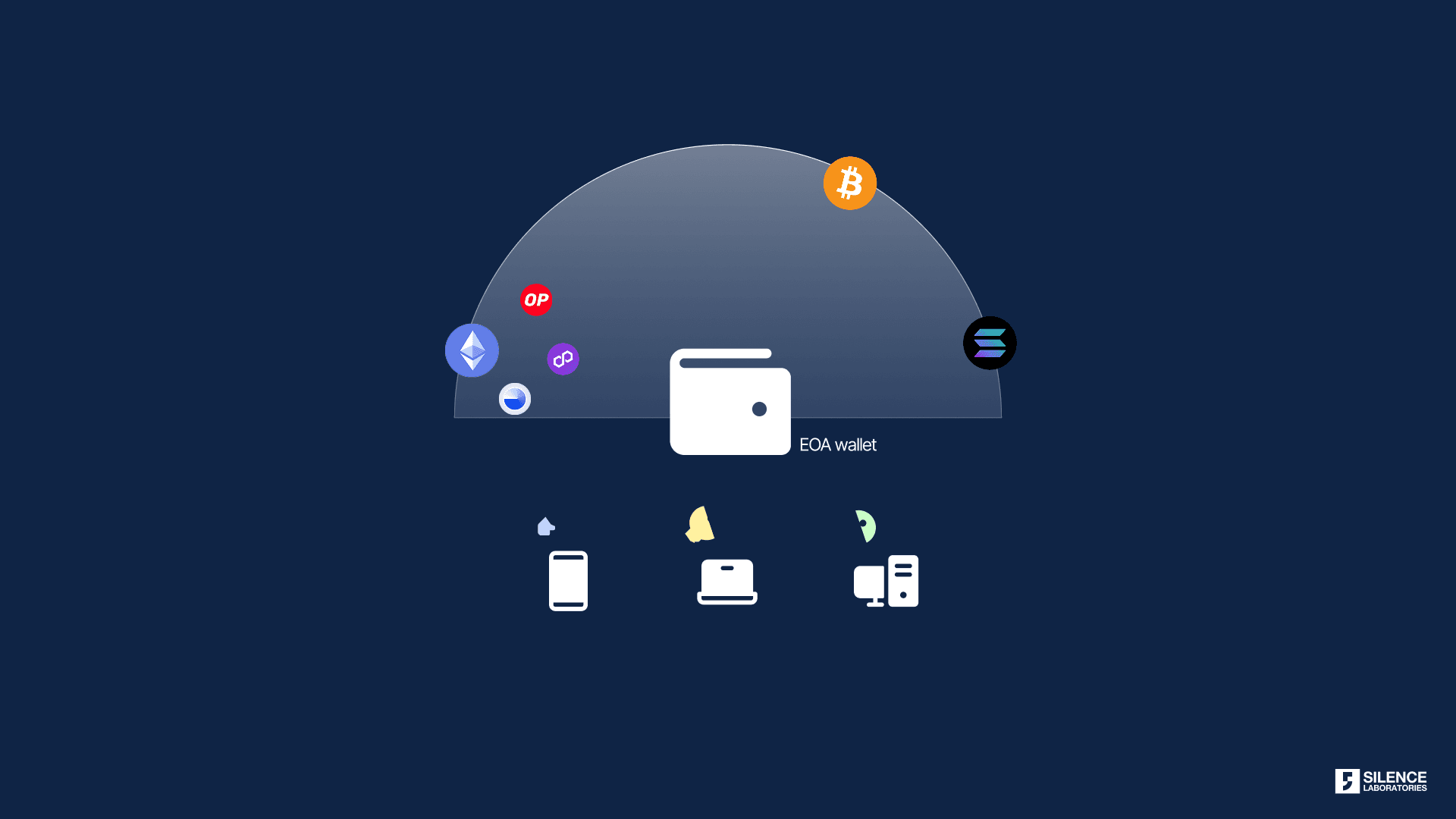
A simple MPC configuration : key-shares distributed across 3 devices.
1. Securing the EOA Private Key 🔐 : In the EIP-7702 model, the EOA’s private key remains the ultimate root of trust for authorizing these temporary smart contract capabilities. Unlike fully smart contract accounts (like those envisioned by EIP-4337) which can implement diverse key management schemes (e.g., fully-social recovery, hardware security modules as multi-signers), the EOA key itself, if compromised, allows an attacker to authorize malicious delegations. MPC directly tackles this by eliminating the single point of failure associated with a single private key — no more putting all your eggs in one basket. By sharding the private key and distributing these shares among multiple, non-trusting parties (or devices controlled by the user), no single share can compromise the key. Signatures are generated through a distributed process where shares are combined cryptographically without the full key ever being reconstructed in one place. This dramatically enhances the security of the EOA wielding EIP-7702’s power.
2. Intelligent Transaction Scrutiny via Off-Chain Policy Engines 🛡️ : Perhaps the most potent application of MPC in the context of EIP-7702 is its ability to integrate sophisticated policy engines that operate off-chain. Before the distributed signing process for an EIP-7702 transaction (or any transaction, for that matter) is completed by the MPC network, the transaction’s intent can be rigorously analyzed against these confidential policies. An integrated policy engine can:
Parse Transaction Payloads: Decode the data to understand which contract is being delegated to and what operations (e.g., function calls, parameters) are intended.
Enforce Pre-defined Rules: Check the transaction against user-defined or institutionally-set policies. For instance, Is the delegated contract on an approved list? Does the transaction attempt to transfer assets exceeding a certain value or to a known risky address? Are the proposed operations within the scope of what the user typically authorizes for a given dApp?
This off-chain, pre-flight check provides a critical layer of defense, directly mitigating the “sign here, drain everything” risk by preventing the MPC network from co-signing delegations that violate established security policies; it’s like having a smart co-pilot for your crypto.
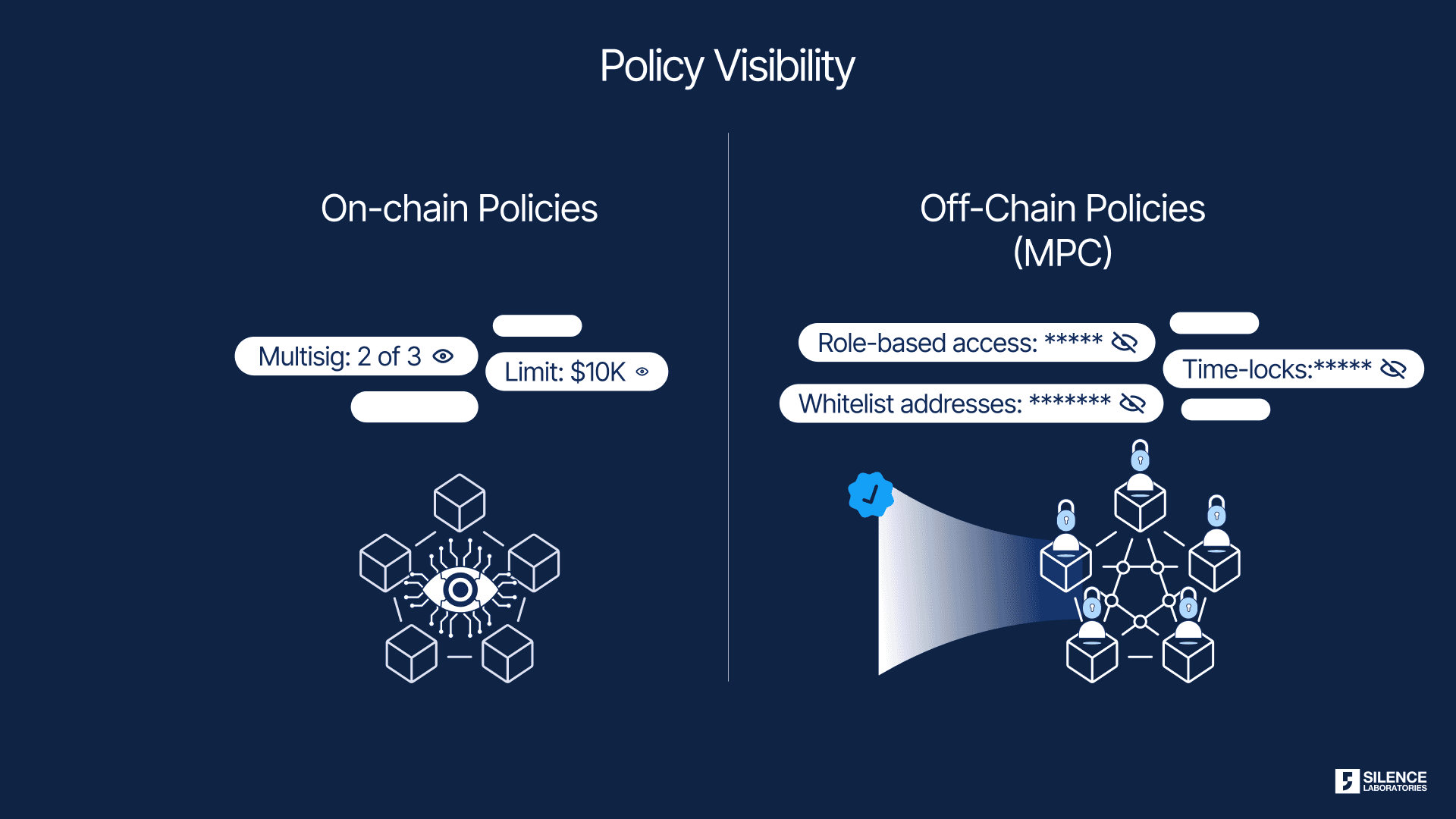
On-chain implies transparancy, off-chain can enable privacy in policies.
3. Unified Multichain Policy Management through Off-Chain Abstraction 🕸️ : The challenge of maintaining consistent security and operational policies across multiple, disparate blockchains is a significant pain point for users and institutions. Each chain may have different smart contract languages, different account models, and varying (or non-existent) native policy enforcement capabilities. MPC, being an off-chain and blockchain-agnostic cryptographic technique, offers a powerful solution here. By leveraging an MPC network with an integrated off-chain policy engine, as discussed above, organizations can define a single, comprehensive set of security and transaction authorization policies that are applied consistently, regardless of the destination chain.
Our flagship Silent Network, for example, is designed to manage key shares and evaluate transactions against such off-chain policies before authorizing any on-chain action. This means that whether a transaction is destined for Ethereum, an EVM-compatible L2, or a completely different non-EVM chain, the same robust, confidential policies are enforced by the MPC layer. This approach drastically simplifies multichain operations, reduces the risk of policy gaps between chains, and provides a unified control plane for managing digital assets across a diverse blockchain ecosystem. MPC, in this sense, acts as a universal policy adapter, ensuring consistent governance without needing to replicate complex logic on every individual chain.
Silent Network & Silent Shard: Next-Generation MPC for an Abstracted Ethereum 🚀
At Silence Laboratories, we are pioneering this advanced application of MPC with our solutions, Silent Shard and Silent Network — we are actively building the future, not just theorizing about it. Our Silent Shard technology provides the foundational MPC-based Threshold Signature Scheme (TSS), which can operate as an Actively Validated Service (AVS). This technology underpins the core distributed key generation (DKG) and distributed signing processes, critically ensuring that private keys are never exposed in their entirety.
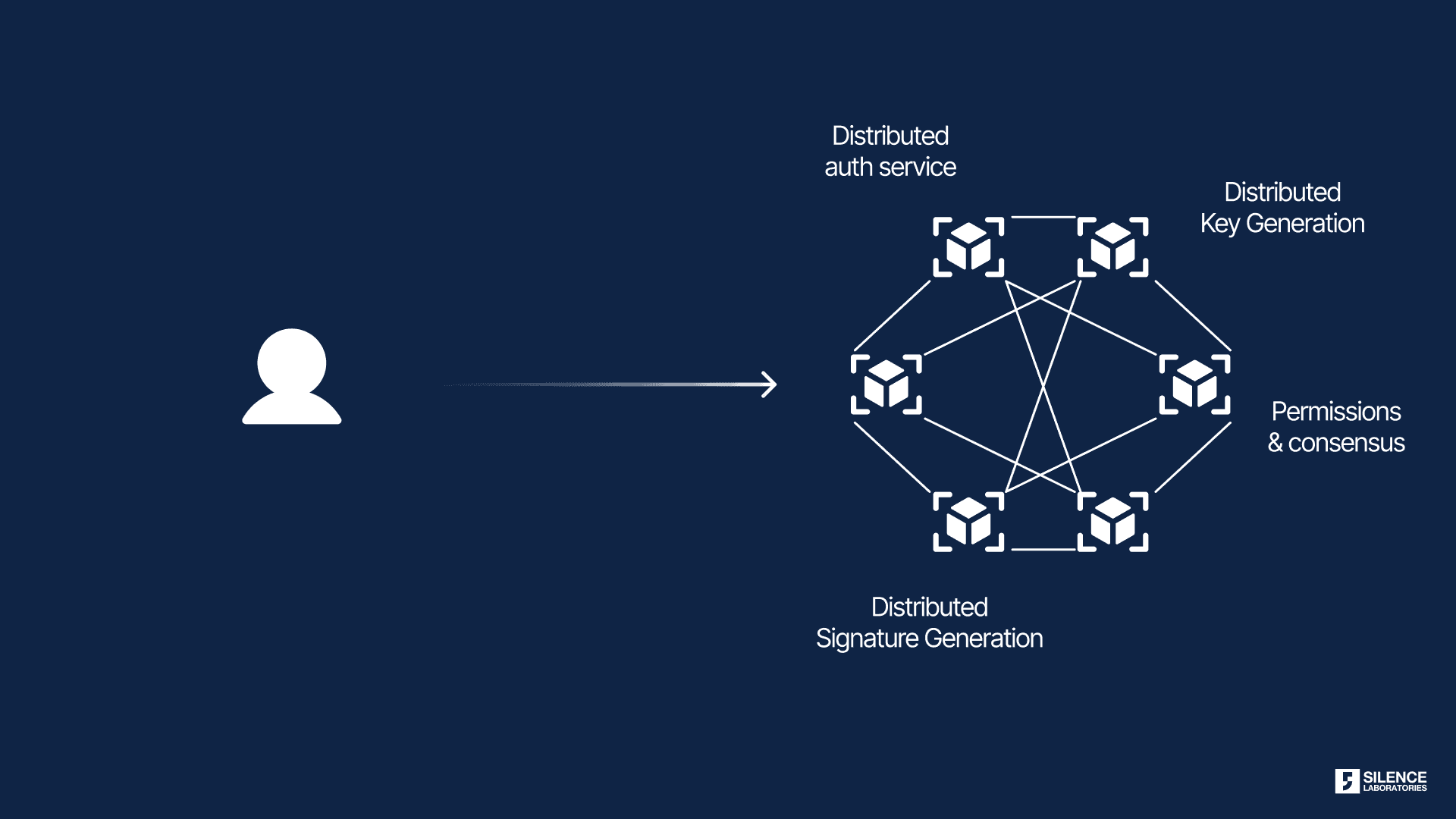
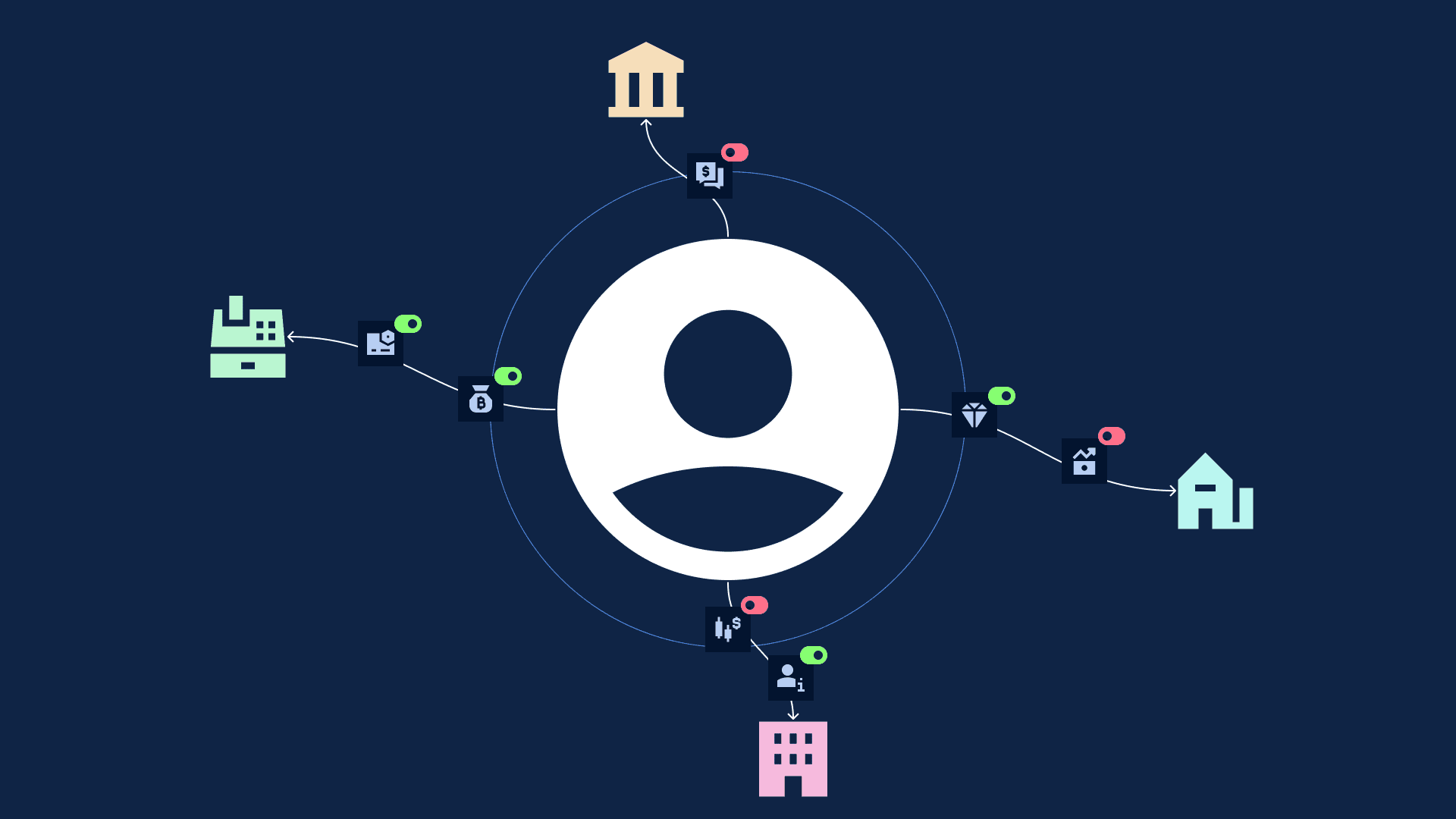
A distributed MPC network (our flagship, Silent Network) can enable secure features
Building upon this robust MPC-TSS foundation, our Silent Network delivers a comprehensive security and usability layer for blockchain interactions. Specifically in the context of EIP-7702, we designed Silent Network to offer several key advantages:
Enhanced EOA Security: The EOA private key, which authorizes EIP-7702 transactions, is secured using our MPC protocols, distributing its shares and removing single points of failure.
Policy-Driven “Session Key” Experience: We’ve engineered Silent Network to implement a powerful off-chain policy engine. Because these policies are enforced off-chain by the Silent Network nodes before any on-chain transaction is constructed, this approach is highly cost-effective, avoiding on-chain gas fees for policy checks. When a user intends to interact with a dApp using EIP-7702, they can approve a “session” with specific parameters. These parameters translate into these off-chain policies. For example, a session might permit interactions only with certain verified smart contracts of a dApp, limit transfer amounts for that session, or restrict the types of functions that can be called — we empower users to set the rules of the game, consistently and economically across all their blockchain interactions.
Proactive Threat Mitigation: If an EIP-7702 transaction attempts to delegate to a malicious contract or perform actions outside the approved session policies, our Silent Network nodes are designed to refuse to co-sign. This effectively blocks the dangerous transaction before it reaches the Ethereum network, directly addressing the policy transparency and “sign here, drain everything” risks associated with EIP-7702 by providing intelligent, off-chain scrutiny.
Improved User Experience: By abstracting away the cryptographic complexities and providing clear policy controls through a unified interface, we aim for Silent Network to offer a user experience that feels akin to secure session management in Web2, making advanced Web3 interactions safer and more intuitive.
Imagine a user wanting to engage in a complex DeFi strategy. Instead of blindly signing a potentially opaque EIP-7702 transaction, they would interact via an interface leveraging Silent Network. Our system would ensure their EOA key is protected by MPC and that any EIP-7702 delegation only proceeds if it aligns with pre-defined safety rules and the user’s explicit intent for that particular “session” with the dApp or be it any EOA based transaction — that’s what we call enabling users to sleep well at night.
Conclusion: Building a More Secure and User-Friendly Ethereum with MPC 🏗️
The Pectra upgrade, and EIP-7702 within it, represent exciting progress towards a more user-friendly and powerful Ethereum; they’re definitely pushing the ball forward. They promise to lower barriers to entry and enhance the capabilities of everyday user accounts. However, these advancements also underscore the critical need for robust security solutions that can manage the new complexities and potential risks they introduce.
Multi-Party Computation is rapidly emerging as an indispensable technology in this new era. By securing the foundational private keys, enabling sophisticated off-chain policy enforcement that works across chains, and offering a path to seamless multichain interactions, MPC provides the essential safeguards required to harness the full potential of innovations like EIP-7702; it’s quickly becoming the bedrock of real security.
Know more about our MPC TSS products that we talked about in this article:
👉🏻 Silent Shard
👉🏻 Silent Network
Our team is always available for a discussion! Come say hi to us :) 👋
Follow us on X — https://x.com/silencelabs_sl