Silence Laboratories & Equal Launch Silent KYC: India's First User-Controlled Privacy Preserving Identity & Data Wallet Infrastructure
An interoperable, privacy-first protocol where verification replaces disclosure, and users own their data, completely.

Written by
Kush Kanwar
Announcement
May 4, 2026

SHARE
Silence Laboratories and Equal launch Silent KYC, a privacy-first, interoperable & user-controlled identity & data protocol where verification replaces disclosure, and users truly own their data.
Today’s KYC experience is repetitive and invasive. Every application, whether for a loan, insurance, or onboarding, requires users to repeatedly share sensitive documents like identity proofs, address records, employment details and income data. Once shared, this data often travels beyond its intended purpose, with little visibility or control for the user.
Built on top of the India stack, Silent KYC reimagines this model entirely.
FROM DATA SHARING TO PROOFS & INFERENCES
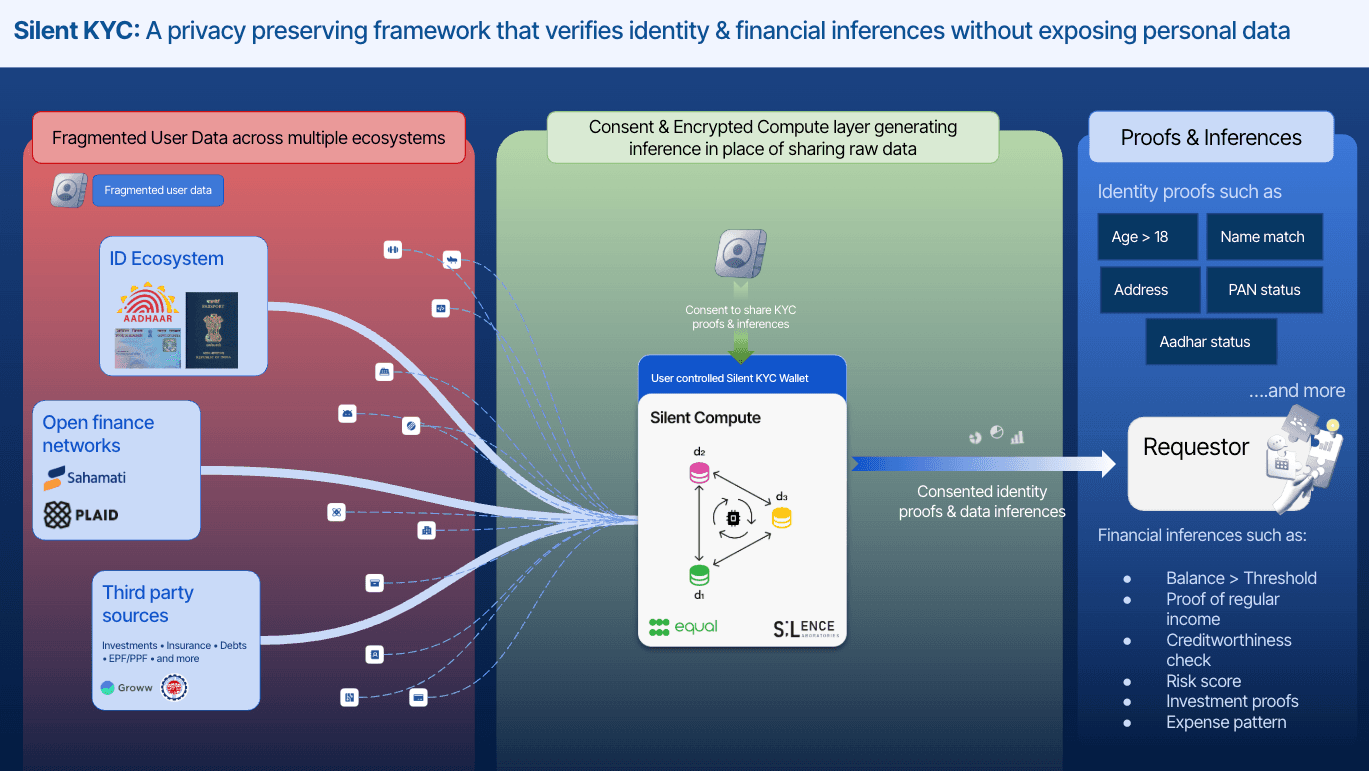
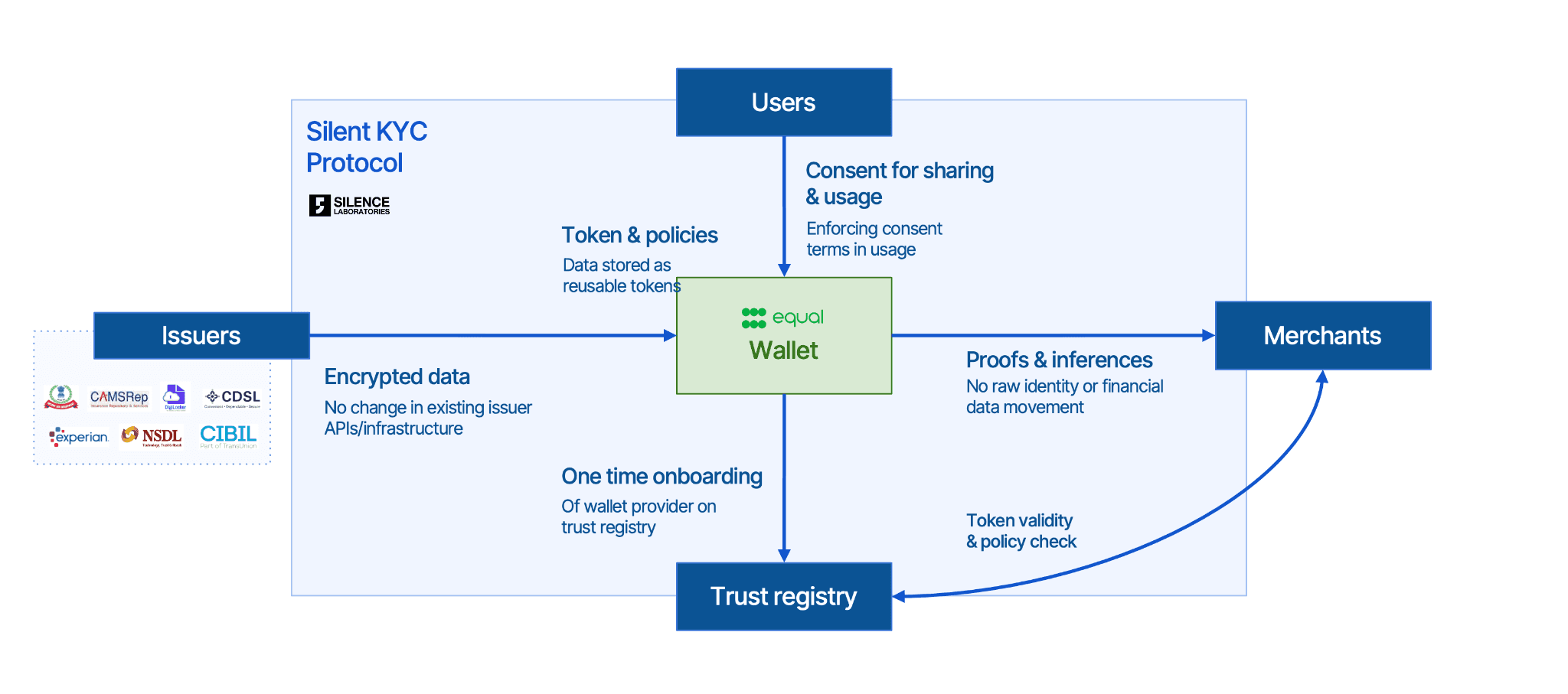
Instead of transferring raw data, Silent KYC enables institutions to receive cryptographically verified proofs and computed inferences. Users create reusable identity and financial credentials once, and only the minimum required information is shared, strictly aligned to the purpose they approve. Raw data never leaves the source, not to the requesting institution, not even to the verification provider.
This fundamentally shifts KYC from a data-transfer mechanism to a privacy-preserving verification layer, reducing friction for users while enabling institutions to access more reliable signals from trusted issuers like UIDAI, DigiLocker, CKYC, NSDL, Account Aggregator and other networks.
RIGHT TO WIN
At the core of Silent KYC is Silence Laboratories’ Cryptographic Computing Virtual Machine (CCVM), powered by Multi-Party Computation (MPC) and Zero-Knowledge Proofs (ZKP).
Data is processed in fully encrypted form
Only the approved output (proof/inference) is revealed
It is mathematically impossible to access anything beyond consented usage
This eliminates the need for centralised data vaults or trusted intermediaries, replacing them with cryptographic guarantees of privacy and purpose limitation.
Silent KYC is not a proof of concept. The protocol has been natively integrated and tested across the Indian Account Aggregator framework, US Open Banking providers including Plaid, and cross-border data frameworks. It was deployed in Project Mandala with the BIS, and won the G20 2025 TechSprint jointly organised by the South African Reserve Bank (SARB) and the BIS for enabling cross-border credit data portability with Proxtera.
"The goal wasn’t to replace existing ecosystems, but to strengthen them, so institutions can collaborate and verify, without ever needing to see the underlying data"

Jay Prakash
CEO & Co-founder, Silence Laboratories
CUTTING EDGE CRYPTOGRAPHY MEETS EXTENSIVE DISTRIBUTION & ISSUER INTEGRATION
Equal provides the user-facing wallet infrastructure that makes Silent KYC practical and scalable. Through the Equal wallet, users create their credential tokens once, manage consent across institutions, delegate access, revoke at any time, and reuse verified credentials without repeating the process.
Equal also brings 1.5B+ annual data transactions and 350+ enterprise customers - the distribution infrastructure that makes Silent KYC immediately deployable at scale.
Rajeev Ranjan, Co-Founder of Equal adds - “From a user’s perspective, identity today feels repetitive and intrusive. We wanted to build something that gives control back to the user, where you share once, and decide how it’s used every time after”
A NEW STANDARD FOR KYC, IN DESIGN AND APPLICATION
Silent KYC is designed fundamentally differently from traditional systems. There is no exposure of raw data and no disruption to existing issuer infrastructure, data remains at the source while verification happens securely. More importantly, consent is tied to computation itself, meaning only permitted computations can execute, and nothing beyond. It is mathematically provable control over how data is used.
Beyond simple identity proofs, this unlocks richer, privacy-preserving inferences, such as income verification or risk signals, expanding the scope of KYC from verification to intelligent, secure decisioning and consequently reducing identity related fraud risks.
Silent KYC strengthens existing workflows while unlocking entirely new use cases. It enables better underwriting in lending and insurance through verified income and behavioural signals, stronger fraud and risk detection using cross-source insights, and opens up new possibilities like income verification for gig workers without formal documents, seamless rental and travel checks without document sharing.
Get started with Silent KYC today, where trust is built on cryptography, not data exposure, and users are firmly in control of their identity.
Learn more about the tech in our deep dive.

